On Tuesday, Wikileaks published what it says are files related to the Central Intelligence Agency’s hacking operations. Apparently the first in a series dubbed “Vault 7” by Wikileaks, the transparency organization claimed the dump was the largest-ever publication of confidential documents concerning the CIA.
“The first full part of the series, ‘Year Zero’, comprises 8,761 documents and files from an isolated, high-security network situated inside the CIA’s Center for Cyber Intelligence in Langley, Virginia,” Wikileaks’ press release reads.
Videos by VICE
According to Wikileaks, the “Year Zero” cache includes information related to dozens of zero-day exploits developed for use against Apple iPhones, Google’s Android operating system, and Microsoft’s Windows. But Wikileaks has not publicly distributed the exploits themselves, according to the press release, avoiding that “until a consensus emerges on the technical and political nature of the CIA’s program and how such ‘weapons’ should [be] analyzed, disarmed and published.”
Wikileaks has also redacted what it says are CIA targets and machines used to launch attacks in Latin America, Europe, and the US.
In the dump, Wikileaks includes the logo of the CIA’s Information Operations Centre. According to a 2015 article from The Business of Federal Technology, this centre is focused on analyzing foreign threats to US computer systems.
According to one page in the cache, the IOC “develops software exploits and implants for high priority target cell phones for intelligence collection. The completed software implants must be tested on an exact version (hardware and software) of the target phone to ensure correct operation and stealth.”
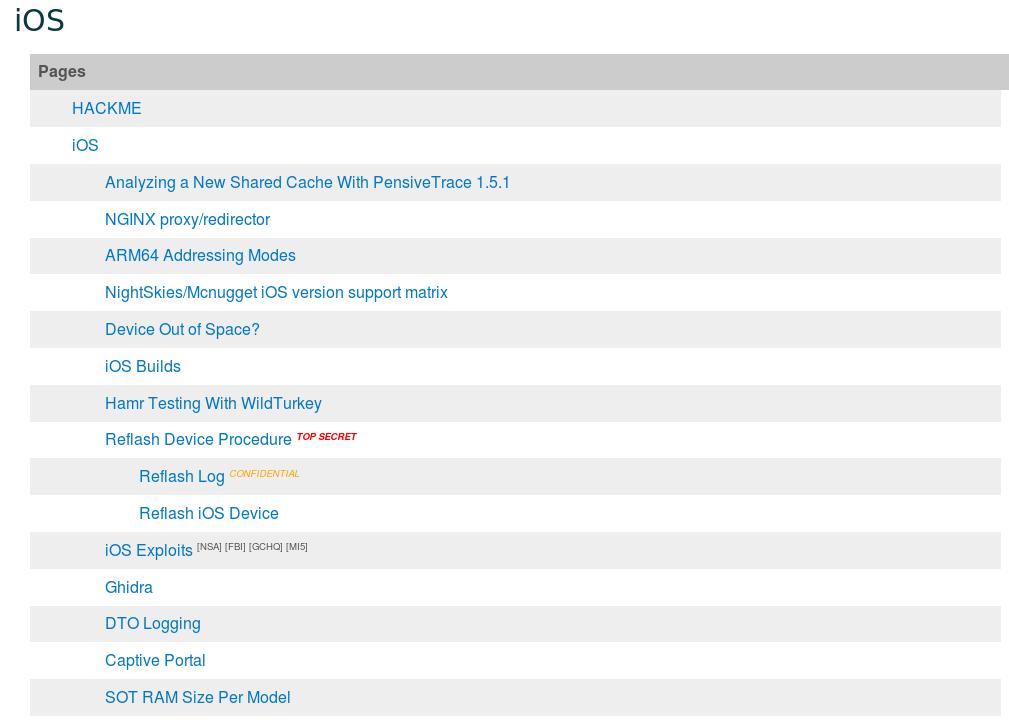
A directory overview of some of the iOS-related documents in the cache.
Other sections of the cache claim to show the sharing of iOS data between different government agencies. In one example, “Earth/Eve”, a remote exploit, was allegedly purchased by the NSA, shared with CIA, and also worked on by GCHQ, the UK’s primary signals intelligence agency. The FBI’s Remote Operations Unit, one of the bureau’s hacking divisions, is also mentioned in another case.
Before the announcement, Wikileaks distributed a 530MB encrypted folder, and then tweeted the archive’s passphrase at around 9AM Eastern Time: “SplinterItIntoAThousandPiecesAndScatterItIntoTheWinds.”

An initial search of the dump contains references to Samsung’s Smart Hub, one of the company’s smart TV products; various versions of iOS, and a wide range of Android devices.
Last year, hackers publicly released working exploits stolen from the National Security Agency. The Shadow Brokers distributed tools for targeting hardware firewalls. The group said it was calling it quits after failing to secure any substantial returns for an attempted crowd-funding release of the rest of their stolen exploits.
As for the alleged CIA dump, Wikileaks claims a former US government hacker or contractor provided portions of the archive.
“The source wishes to initiate a public debate about the security, creation, use, proliferation and democratic control of cyber weapons,” Wikileaks’ press release reads.
The CIA did not respond to Motherboard’s request for comment.
Subscribe to pluspluspodcast, Motherboard’s new show about the people and machines that are building our future.




