Jihadis and their supporters have long made use of encryption to communicate securely, and in some cases even make their own, branded versions of encryption tools. Recently, however, some apparently jihadi-inspired developers took a noticeable step: they designed a custom tool hiding encrypted messages inside an image.
Although the effectiveness of the program, dubbed Muslim Crypt, is unclear, it still shows that some alleged supporters are trying to push extremists’ communications into more potentially difficult to monitor spaces.
Videos by VICE
“Alhamdulillah [praise to God]!! Please test and make suggestion for what else can be improved by our team. We are glad to have a release for you now,” a recent message from an administrator of a Telegram channel called MuslimTec reads. Raphael Gluck from research group JihadoScope, which provided a copy of the program to Motherboard, said the Telegram group shared a screenshot of a beta of Muslim Crypt around two weeks ago. The channel has exhibited some Al Qaeda and Islamic State-related material.
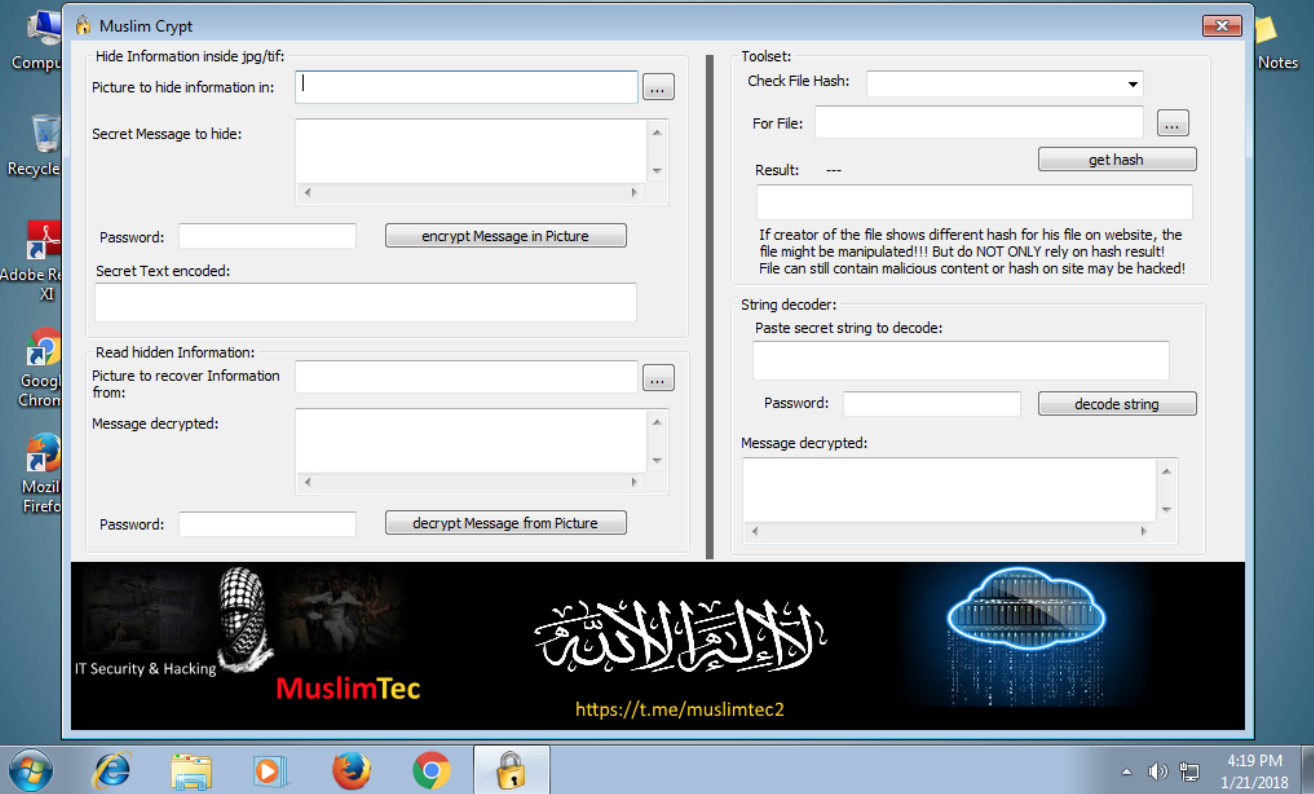
The program’s presentation is basic, with fields to enter which image should be used, the message to hide, and then to enter a password. Naturally, another section of the interface is for decrypting messages, and another part also streamlines the process of checking a ‘hash.’ A hash is a long string of characters that acts as a fingerprint of a file. If the file is altered in any way, the hash will be different as well, letting users check whether someone has tampered with whatever they want to download, be that an image, program, or something else.
“Sometimes you might need to have an option. And best is not to use kuffar [nonbelievers] program with all the spy looking into your communication. Unknown program with heavy encryption is good to go in times of trouble and no paper can be used,” one of the members of the group recently wrote on Telegram, according to messages JihadoScope shared with Motherboard.
“There’s no good reliable technique to find this stuff if the data is encrypted and the techniques are smart. It just looks like noise, and photos have a lot of noise.”
These supporters are probably pretty misguided though. Not only do some cryptographers generally agree that creating your own encryption mechanisms is dangerous—cryptography is, well, really hard to get right—but having a custom solution may stick out much more than just using a tried-and-tested product that the general population uses too. An earlier jihadi-encryption program called Mujahideen Secrets, for example, blasts “Begin Al-Ekhlaas Network ASRAR El Moujahedeen V2.0” at the top of each message; an indicator that intelligence agencies should easily be able to pick up on. Of course, some of the branding and brazenness of making messages stand out might be intentional: This is proudly our means of communication, the people using this technology might think.
Hiding messages in images, called “steganography,” may be slightly more subtle than sending messages through text, though. With steganography they may be able to hide messages in more innocuous images and post them openly, meaning only those with the right program can decipher their contents.
“There’s no good reliable technique to find this stuff if the data is encrypted and the techniques are smart. It just looks like noise, and photos have a lot of noise,” Matthew Green, a cryptographer and Assistant Professor at the Johns Hopkins Information Security Institute told Motherboard in a Twitter message, referring to steganography generally. However, the developers behind custom jihadi apps may not be all that qualified.
“But obviously most of the time the people doing it aren’t that smart, and so that stuff can be found,” Green added.
The creation of programs such as Muslim Crypt also highlight the futility of law enforcement hopes to ban the use of unbreakable encryption in popular hardware and messaging apps. Extremists, and perhaps criminals, are going to develop or source their own solutions.
The Telegram username included in an image embedded at the bottom of Muslim Crypt’s interface was not reachable for comment: at the time of writing, no such user exists, suggesting Telegram may have deleted their account.
A recent message in the MuslimTec group suggested users test Muslim Crypt against anti-virus software, presumably to double-check that the program isn’t malicious. (According to the results from an online malware analysis service, Muslim Crypt does contain the ability to record keystrokes, but several malware experts told Motherboard not to take that result at face value).
“We are working on a more advanced MuslimCrypt version. The pinned version is a first release, but not the final one,” another recent message on Telegram reads.
More
From VICE
-

CSA Images/Getty Images -

Illustration by Reesa -

Screenshot: GSC Game World -

Screenshot: Bethesda Softworks
